Rippling
Rippling is an HRIS.
While exploring Rippling, I have to say something interesting about their product.
Org Chart as an Analogy for Polykey Enterprise
This Rippling's org chart - it shows as the glance who is working in the company, their role, their responsibilities. This can make it easier to understand the human resources within a company.
The Node Explorer by comparison is like an org-chart - but focuses on the dimensionalities and properties of authority - either from a human agent perspective or autonomous agent perspective
Rippling SSO as an Authority/Capability Box
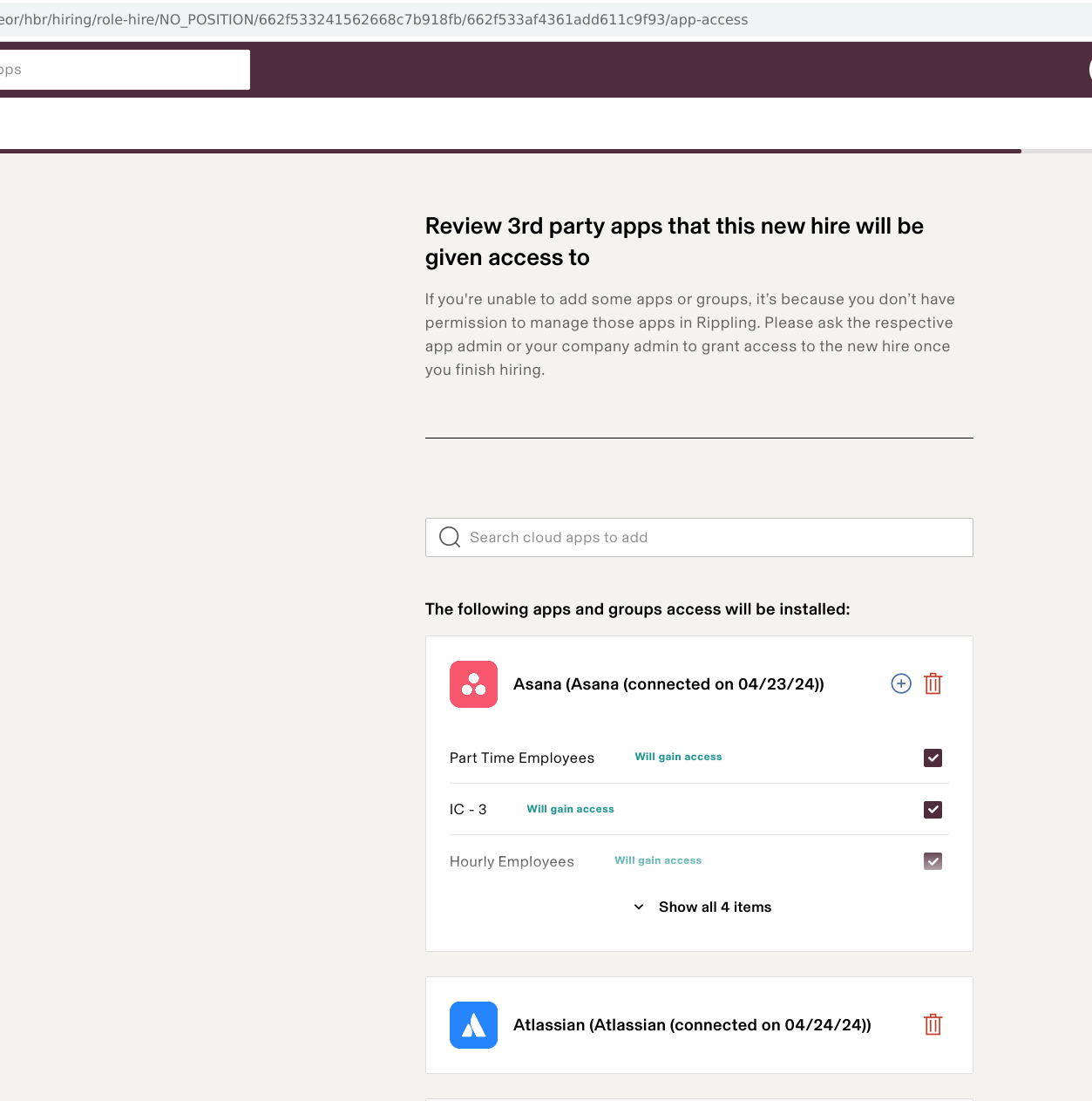
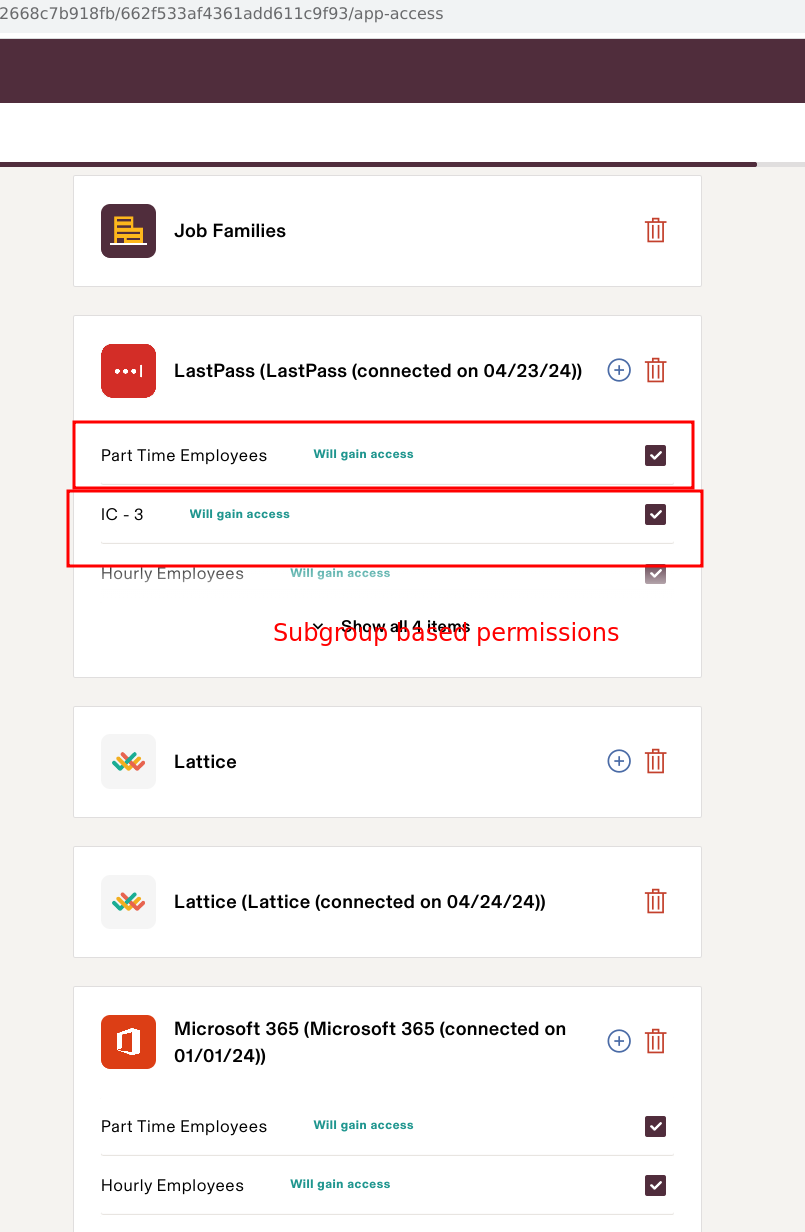
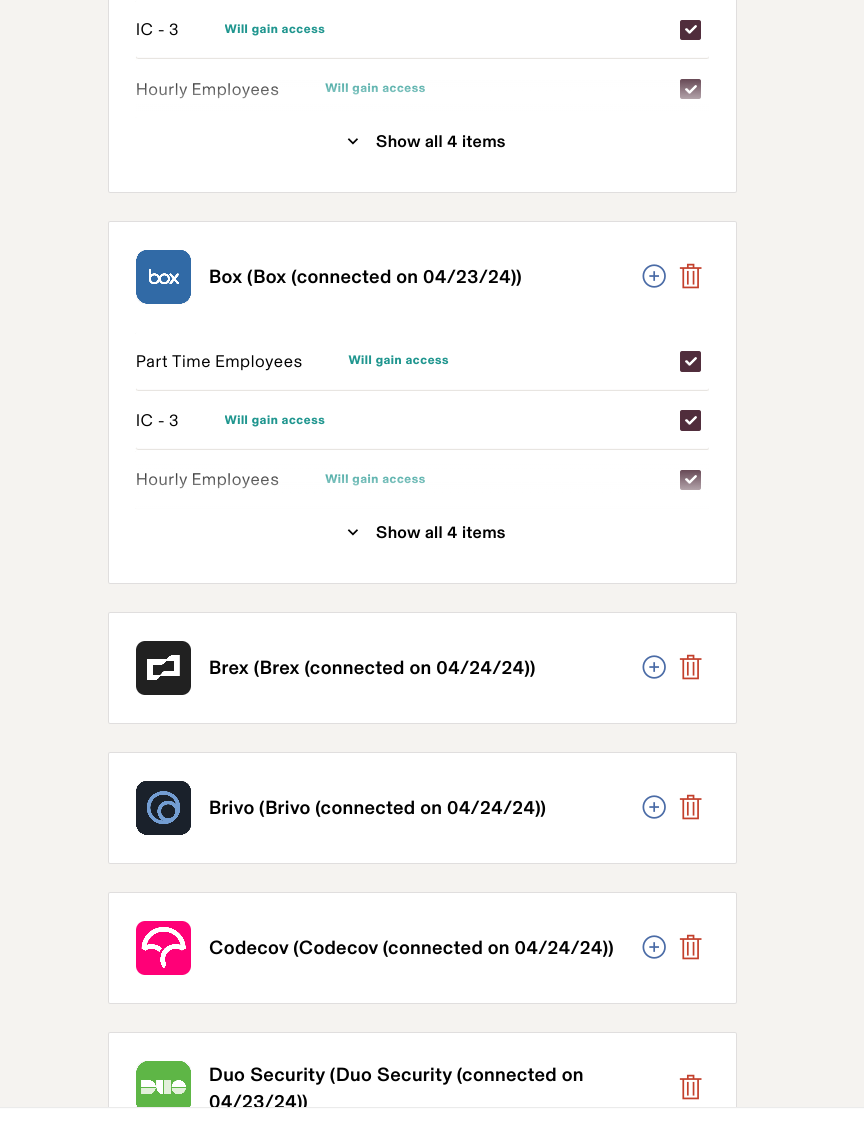
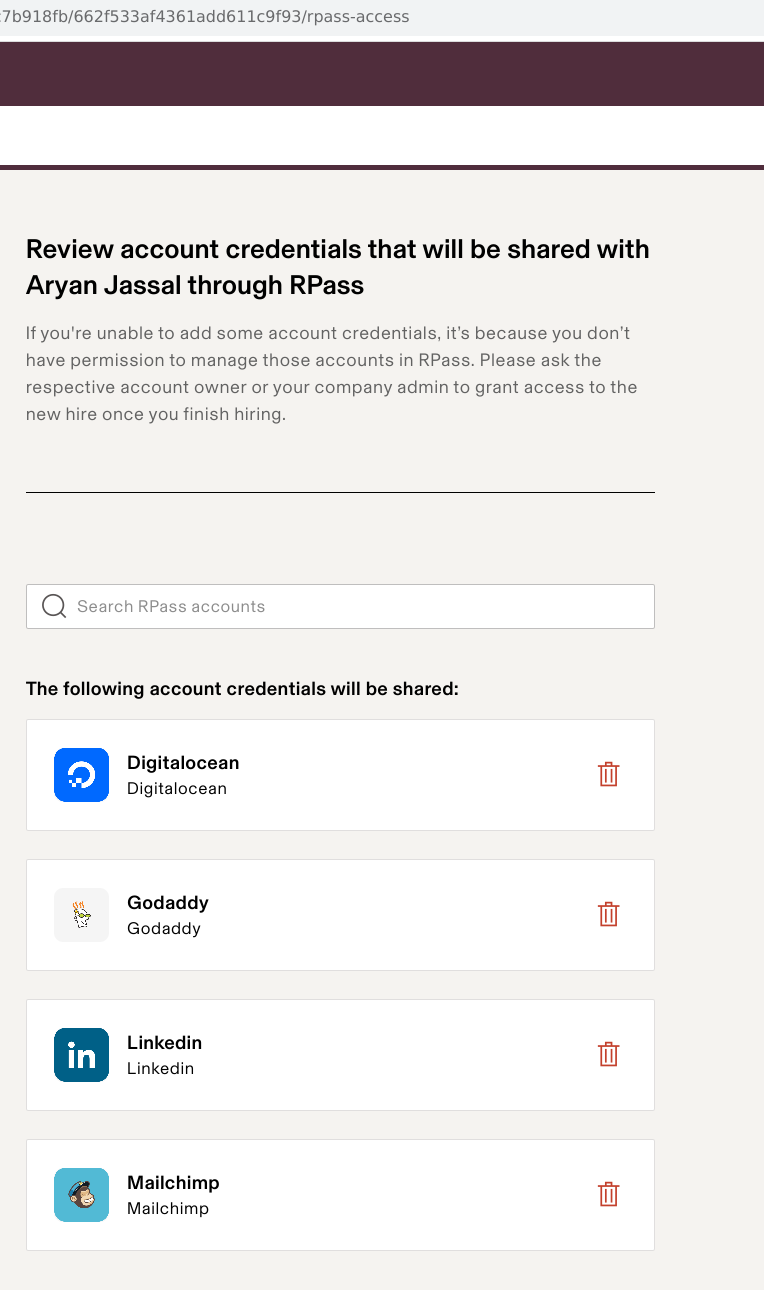
Here's an example of authority delegated via onboarding on SSO systems.
Some initial thoughts:
- This is works because Rippling creates an SSO service and acts as cloud identity provider for the companies that sign up - but how does rippling deal with companies that have their existing IdPs? What if the company is using Microsoft active directory, or LDAP, or just has used like GitHub org as their IdP (like we are right now).
- Rippling SSO only works if you integrate its IdP with SSO-protected resources. Most services tend to price their SSO-protection at an enterprise level, which means it's often not self-serve, thus price-differentiated to an enterprise market.
- The SSO authority delegation is geared towards human-agents, rather than machine-agents - this has implications given the that PK focuses on autonomous agents as much as human agents - are all machines ultimately deriving their authority from a "person"?
- Human agent is really just an assumed account - but an account itself is self-recursive, it could represent a group, but it's not exactly designed for it. Group authority is not a thing here.
- It's interesting that it's possible to automate some of the logical flows for authority - by creating "groups" or other properties of identities that then flow onto resource-specific rules in these applications - I wonder what standard they follow here. For example can a shared property of identity in Rippling propagate to team/group association on GitHub?
- Offboarding wise, this certainly makes it convenient to prevent access when the identity is offboarded rather than chasing down every account to remove authority. However how does this impact machine authorities, or authorities sitting outside of these application gateways? Suppose PK provided capability proxies, so that even keys are decommissioned.
- More than 3 years ago, Mark was always confused about what PK is, especially in relation to SSO - his entire contextual understanding of enteprise cybersecurity was in this field, because as sales person he never deal with autonomous agents. So we never could bridge the gap in understanding.
- Being able to visualise not only what authority an employee has - but going one layer deeper by inspecting the sub-rules within each application - and potentially going even deeper than that would be very interesting, and applicable to the design of the Node Explorer. But this requires standardisation of the identity-authority policy - and I'm not sure if SSO nor anything has become a main standard, so this might be subject to the MxN problem of scalability
- ... more
I will want to integrate this into the discussions around PKE.
Details
Rippling SSH Manager
It's interesting that the whole IdP comes back online. If you use Rippling SSO, and you use it as the IdP for your company, your IdP via SSO can be presented via the API of LDAP, FreeIPA or Active Driectory. In doing so, you can integrate into Linux PAM module. This federates Linux login process with corporate identity systems. Thus PAM is the way Linux integrates with "SSO" sort of systems.
How does this compare with SSH Certificates? How it reminds me back of the research I did in Authentication vs Authorisation. I should bring that out again.